MSDN官方文档给出的定义:
HHOOK SetWindowsHookEx( int idHook,
HOOKPROC lpfn,
HINSTANCE hMod,
DWORD dwThreadId
idHook:挂钩类型,即处理的消息类型;我此处测试的是WH_KEYBOARD
lpfn:挂钩函数的地址指针。如果是全局钩子,即dwThreadId为0或者Hook的进程不是当前进程,那么lpfn必须指向DLL中的挂钩函数。除此之外,lpfn可指向当前进程的一段挂钩函数代码。当钩到消息后,执行此函数。为适用性起见,我在代码中用的是从DLL中导出的函数地址。
hMod:应用程序的的实例句柄,指向包含lpfn指针的DLL。
dwThreadId:如果为0,则表示该钩子与所有线程相关联,为全局挂钩。
函数失败,返回NULL,成功返回钩子句柄。
实现思路:
- 从控制台得到想要实施注入的目标进程名字
- 得到当前进程所在的目录(GetCurrentDirectory),并保存
- 得到当前进程的位数 (IsWow64Process)
- 根据进程名字得到当前进程的Id
- 根据进程Id得到当前进程的完整路径
- 通过进程完整路径对PE文件解析得到目标进程位数
- 目标与当前进程的位数进行匹配,决定加载哪一个dll(x86 or x64)
- 根据当前进程目录,得到dll完整路径
- 通过目标进程Id返回目标进程中所有线程的Id
- 通过LoadLibrary加载目标动态库,得动态库模块句柄
- GetProcAddress得到导出函数的函数指针
- SetWindowsHookEx实施对某个线程的注入
- 收尾工作,卸载钩子
#include"SetWindowsHookEx.h"
#include"Helper.h"
int _tmain(int argc, TCHAR* argv[], TCHAR *envp[])
{
setlocale(LC_ALL, "Chinese-simplified");
TCHAR ProcessImageName[MAX_PATH] = { 0 };
TCHAR CurrentFullPath[MAX_PATH] = { 0 };
TCHAR TargetProcessFullPath[MAX_PATH] = { 0 };
ULONG_PTR TargetProcessPathLength = MAX_PATH;
ULONG ProcessId = 0;
vector<HANDLE> ThreadId;
HANDLE ProcessHandle = INVALID_HANDLE_VALUE;
HMODULE ModuleBase = NULL;
FARPROC InjectFunction = NULL;
HHOOK HookHandle = NULL;
BOOL IsOk = FALSE;
BOOL SourceIsWow64 = FALSE;
BOOL TargetIsWow64 = FALSE;
_tprintf(_T("输入一个进程ImageName\r\n"));
TCHAR RcceiveChar = _gettchar();
int i = 0;
while (RcceiveChar != '\n')
{
ProcessImageName[i++] = RcceiveChar;
RcceiveChar = _gettchar();
}
GetCurrentDirectory(MAX_PATH, CurrentFullPath);
IsWow64Process(GetCurrentProcess(), &SourceIsWow64);
ProcessId = KtGetProcessIdentify(ProcessImageName);
if (ProcessId == 0)
{
return 0;
}
IsOk = KtGetProcessFullPath(TargetProcessFullPath,
&TargetProcessPathLength, ProcessId, FALSE);
if (IsOk == FALSE)
{
return 0;
}
KtIsWow64Process(TargetProcessFullPath, &TargetIsWow64);
if (SourceIsWow64 == TRUE && TargetIsWow64 == TRUE)
{
_tcscat_s(CurrentFullPath, _T("\\Dll.dll"));
}
else if (SourceIsWow64 == FALSE && TargetIsWow64 == FALSE)
{
_tcscat_s(CurrentFullPath, _T("\\Dll.dll"));
}
if (KtGetThreadIdentify((HANDLE)ProcessId, ThreadId) == FALSE)
{
goto Exit;
}
ModuleBase = LoadLibrary(CurrentFullPath);
if (ModuleBase == NULL)
{
goto Exit;
}
InjectFunction = GetProcAddress(ModuleBase, "InjectFunction");
if (InjectFunction == NULL)
{
goto Exit;
}
for (int i = 0; i < ThreadId.size(); ++i)
{
HookHandle = SetWindowsHookEx(WH_KEYBOARD, (HOOKPROC)InjectFunction, ModuleBase, (DWORD)ThreadId[i]);
if (HookHandle != NULL)
{
break;
}
}
_tprintf(_T("Input AnyKey To Exit"));
getchar();
Exit:
if (HookHandle != NULL)
{
UnhookWindowsHookEx(HookHandle);
HookHandle = NULL;
}
if (!!(ThreadId.size()))
{
vector<HANDLE>().swap(ThreadId);
}
if (ModuleBase != NULL)
{
FreeLibrary(ModuleBase);
ModuleBase = NULL;
}
}
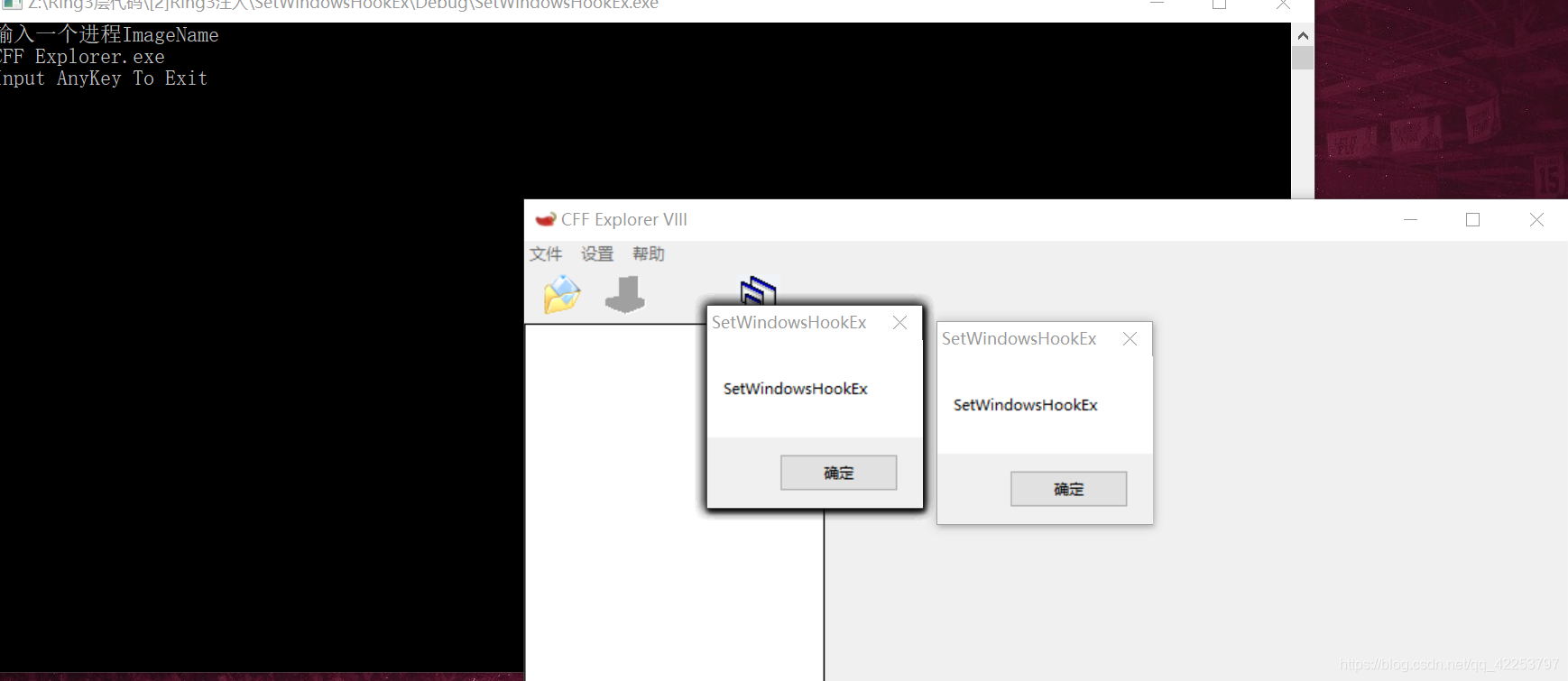
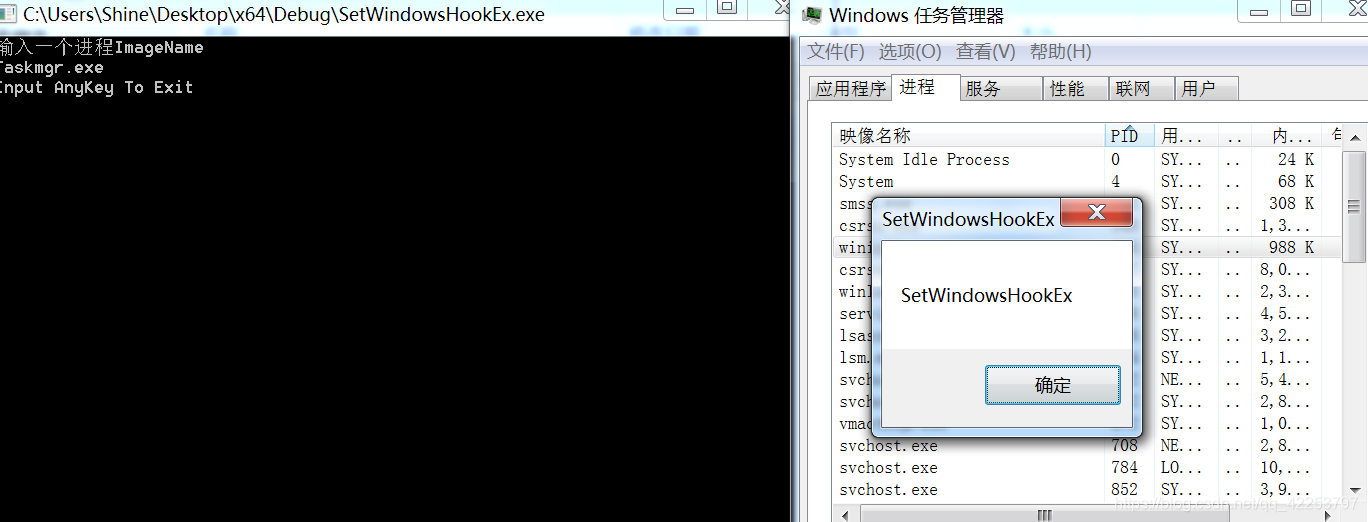
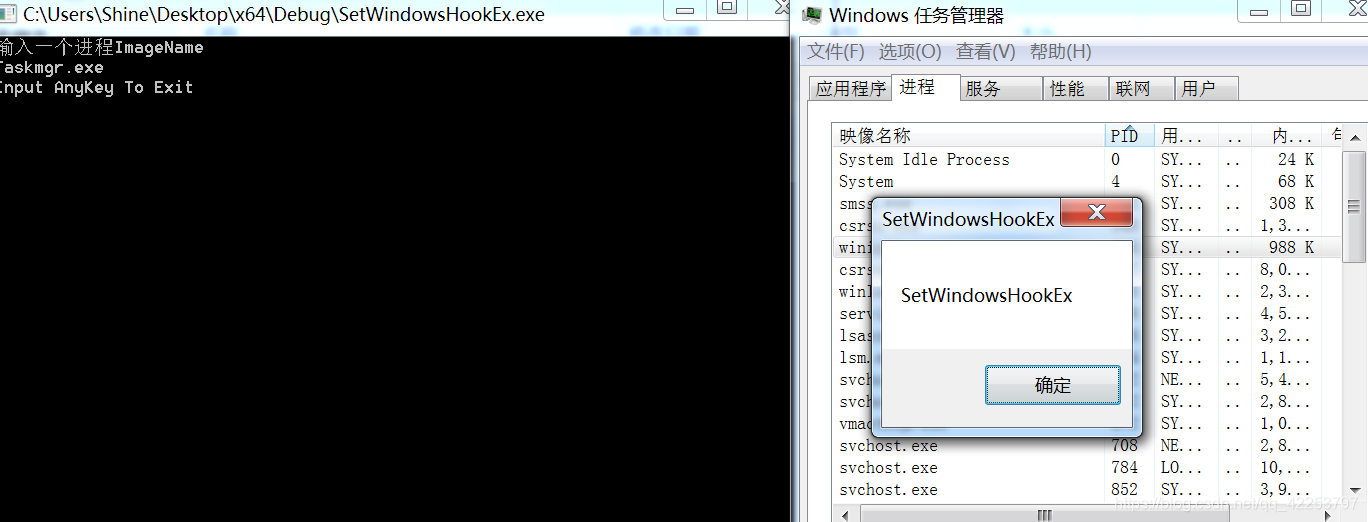
注入成功截图:按键就会产生弹窗效果
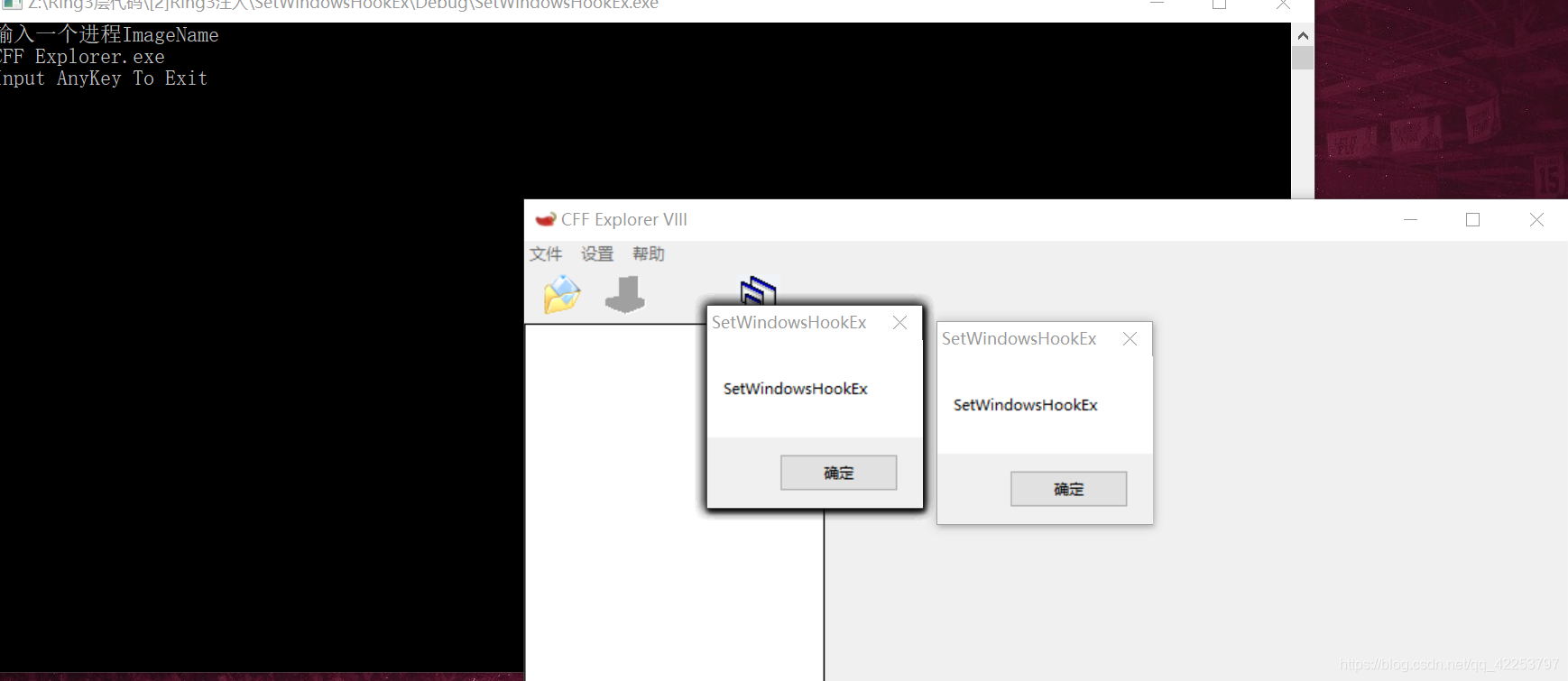
64位测试截图:
卸载之后我也进行了键盘按键,不会弹出来了。
不忘初心,方得始终
cs